Numerous recipients of unemployment benefits in D.C. have received suspicious emails from D.C. government accounts over the last two weeks, indicating a possible intrusion into city computers by scammers attempting to coax confidential information from people with information in official databases.
The emails started going out in mid-August, promising recipients — many of whom have collected unemployment benefits from D.C. during the pandemic — anywhere from $16,988 to $22,988 in additional benefits. All they have to do to collect the money, the scammers say, is reply with additional identifying information about themselves.
Each of the emails was sent from DC.gov accounts belonging to actual city workers, some of whom work for the Department of Employment Services — which handles unemployment benefits — and others who do not. One came from the email address of Darrick Ross, a scuba diver sergeant at the Metropolitan Police Department, and another from the email address of Alesia Henry, an education compliance specialist at the Office of the State Superintendent for Education.
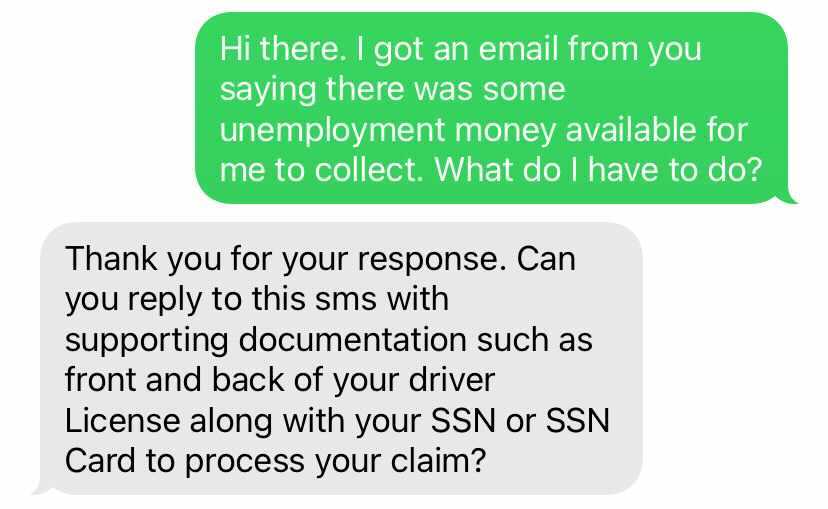
Yet another email was sent from the account of Shanta Suggs, who works at DOES as a compliance investigator. It asked the recipient to text a New York number for further information on how to collect an additional benefits payment. DCist/WAMU sent a text to the number, and received a response requesting copies of “supporting documentation such as front and back of your driver license along with your [Social Security number] or SSN card to process your claim.”
All of those pieces of information can be used to steal a person’s identity, a scam commonly known as phishing. D.C. officials have not disclosed how extensive the scam may be — in terms of the number of spoofed government email addresses or the number of unemployment claimants targeted — but say they have taken steps to freeze the email accounts and contact the people who received the messages.
Emmett, a D.C. resident who asked DCist/WAMU to withhold his last name because of an ongoing legal matter involving his former employer, first received an email from a D.C. government account on Aug. 21 saying he was eligible for almost $17,000 in additional unemployment benefits. Despite not having communicated with DOES or collected any benefits since March, he initially thought the offer was legitimate. But as he checked on the sender’s job title, he started thinking something was “fishy.” He ignored the email, but got a second one a week later. At that point, he called DOES, which said there was no record of any emails being sent to him during that time period.
“I just don’t even know if that means that my personal information is somewhere, or if this is just random. I’m a little concerned, obviously,” Emmett says. “I’m very cautious about security, and even I was like, ‘Oh, this could be legit.'”
The problem isn’t exclusive to D.C. Earlier this month, the Federal Trade Commission warned of phishing schemes nationwide that target people who receive unemployment benefits. Because of the pandemic, the number of recipients and the amount they receive in benefits has increased significantly, offering hackers and scammers a wealth of targets. (More than 228,000 people have applied for unemployment benefits from D.C. since the start of the pandemic.)
“Identity thieves are targeting millions of people nationwide with scam phishing texts aimed at stealing personal information, unemployment benefits, or both,” warned the FTC.
Individuals who did not have contact with the unemployment system also appear to have been targeted. Another person who spoke to DCist/WAMU said they received a similar email after applying for a job with a D.C. agency. (They asked to withhold their name because they’re still under consideration for the job.) Another unemployment claimant in Trinidad — who requested anonymity to discuss sensitive financial matters — received an email requesting proof that she had lost work due to COVID-19. The message came from the address of a DOES employee, but the claimant had no outstanding issues with her payments, and concluded it was fake.
“I just ignored this email, but I think for a lot of people, especially people who have been desperate to get payments, that they would answer it. And to this day, I still haven’t seen anything from DOES saying that they are having a spoofing issue,” they said, referring to an unauthorized use of official email accounts.
That concern is shared by D.C. Councilmember Elissa Silverman (I-At Large), who chairs the council’s labor committee, which oversees DOES. She says her office has been made aware of the emails, and she spoke to DOES Director Unique Morris-Hughes about them.
“I have asked the director for a very robust response from DOES to make people aware,” says Silverman. “I think we need to be more proactive. I’m just not sure what tools we have to be more proactive with.”
In a statement, Lindsay Parker, D.C.’s chief technology officer, said her office was aware of the spoofed emails and was taking steps to ensure that no recipients share identifying information with the scammers.
“The D.C. Office of the Chief Technology Officer investigated reports of compromised D.C. Government email accounts that were used to collect information from members of the public. The team locked the accounts and prevented further action from being taken,” said Parker. “D.C. Government is in the process of contacting members of the public who responded to these compromised accounts so that they can take action to protect themselves.”
Parker added that the city has not been immune to the “continued nationwide trend of cyber criminals taking advantage of UI claimants,” and asked that anyone who receives a suspicious email report it. For her part, Silverman urges people never to share personal identifying information over email or text message.
“That’s the golden ticket for [scammers] when you give them that information,” she says.
The last significant breach of D.C. government computers happened in the spring, when foreign hackers accessed MPD computer systems, stole emails and other documents, and posted them publicly.
 Martin Austermuhle
Martin Austermuhle Ally Schweitzer
Ally Schweitzer



